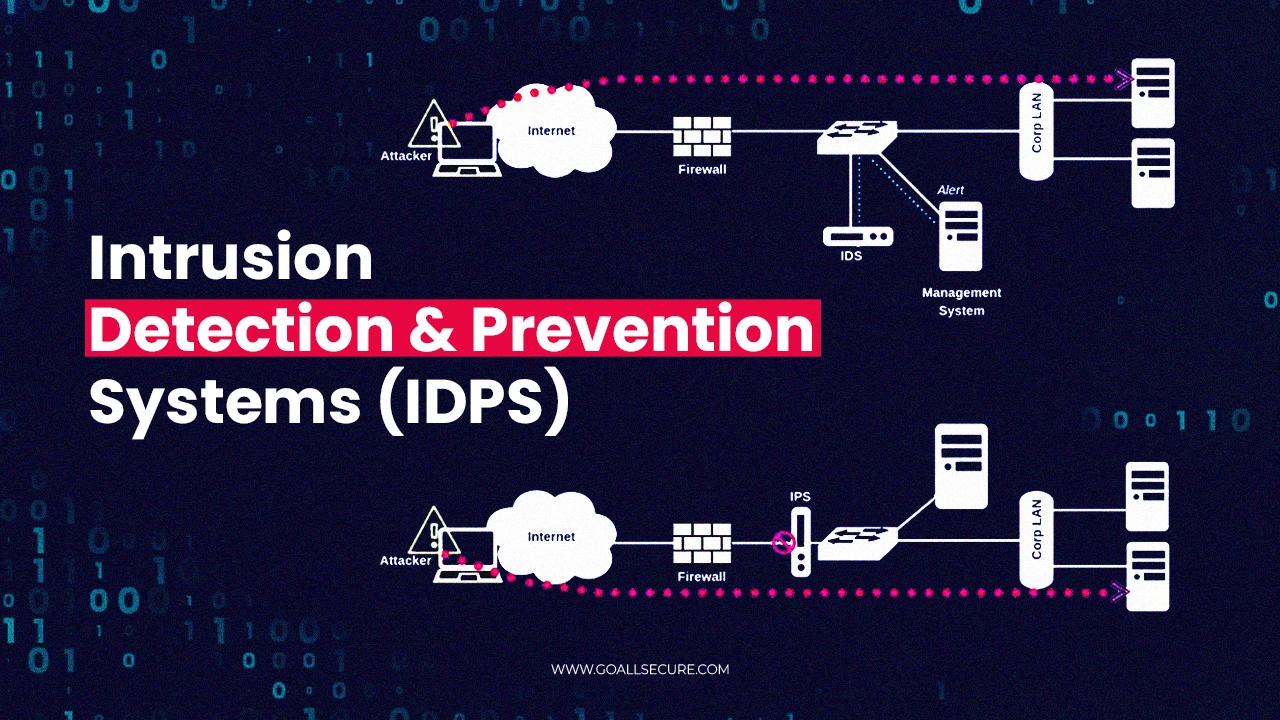
What Is an Intrusion Detection and Prevention System (IDPS)?
The massive increase in cyber attacks and attempts at breaching networks and systems has led businesses to develop defences. One such defence mechanism is IDPS or the Intrusion Detection and Prevention System. It has been around for decades and continues to be an essential component of effective cyber hygiene. This blog will discuss intrusion detection and prevention systems (IDPSs), their significance in network security, their various types and their working.

















 TRAVEL & HOSPITALITY
TRAVEL & HOSPITALITY HEALTHCARE
HEALTHCARE RETAILS & ECOMMERCE
RETAILS & ECOMMERCE BANKING & FINANCIAL
BANKING & FINANCIAL AutoMobile
AutoMobile MANUFACTURING
MANUFACTURING FOOD
FOOD EDUCATION
EDUCATION